Ransomware’s popularity continues to skyrocket, due to its successful business model and the significant profit paid by its victims. Unlike other malware business models – where attackers steal data and then sell it on the darknet; hackers who utilize ransomware as their attack vector receive payment directly from their victims. They do so by disrupting the victim’s environment, and their reward is made possible by the anonymity provided by digital currencies such as bitcoin. The massive WannaCry attack (see Figure 1), which infected tens of thousands computers around the globe, is just one very recent example of a successful ransomware attack, but there were many others before it, and without a doubt there will be many more to come.
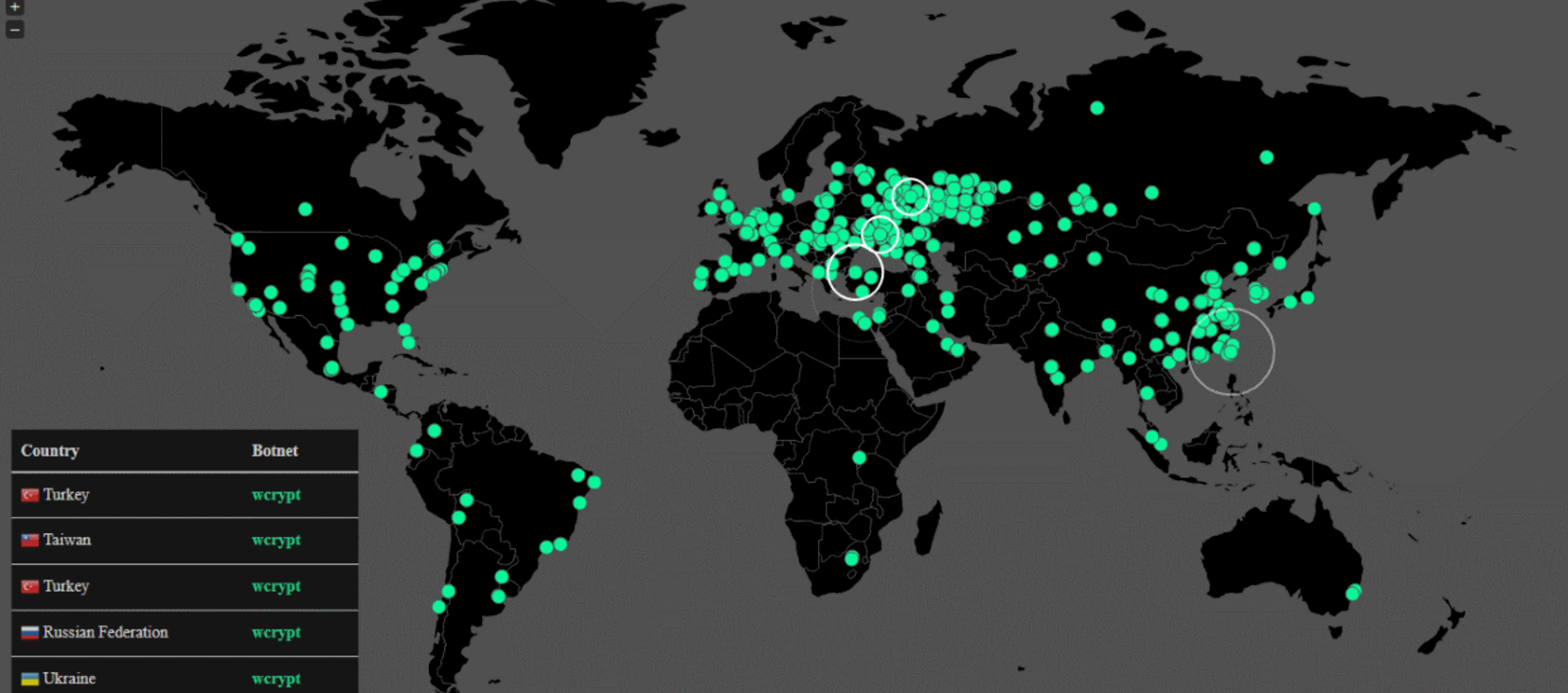
Figure 1: Sample of WannaCry infections seen on May 13, 2017 [Source: MalwareTech]
Additionally, custom-made solutions for laymen such as Ransomware as a Service (RaaS) and do-it-yourself (DIY) kits, which offer out of the box, easy to use tools to launch attacks, are also helping to fuel the growth of ransomware.
While ransomware’s latest incarnations tend to be focused on file encryption (“encrypt, and demand ransom to decrypt”), future versions aren’t likely to rely on that tactic alone. Some attackers already understand that taking files hostage (aka extorionware) is only one method of making easy money.
Attacking—whether the vector is corruption, exfiltration or disruption—then demanding a ransom in order to stop or revert the attack, could very well be the future of the malware landscape. Cyberextortion if you will.
The Future of Ransomware
Here are a few possible attack trends we predict we’ll see moving forward with ransomware:
Data Corruption
File and database corruption: Currently, the most common type of ransomware attack is file corruption (encryption), using cryptographic API. But lately, we’ve also witnessed database corruption attacks (against MongoDB and MySQL for example – see Figure 2) through SQL queries, striking tens of thousands of databases around the world. Ransomware attacks against databases are likely to increase since they are where an organization’s most sensitive data is usually located.
Keep in mind that encryption is only one method of corruption. Corruption can also be:
- A complete files wipeout
- Dropping all database tables
- Any data tampering (e.g., changing database records)
Although don’t be mistaken – file encryption isn’t going away any time soon. The method works, the potential attack audience is large (both individuals and enterprises), and anti-virus solutions do not effectively protect against it.
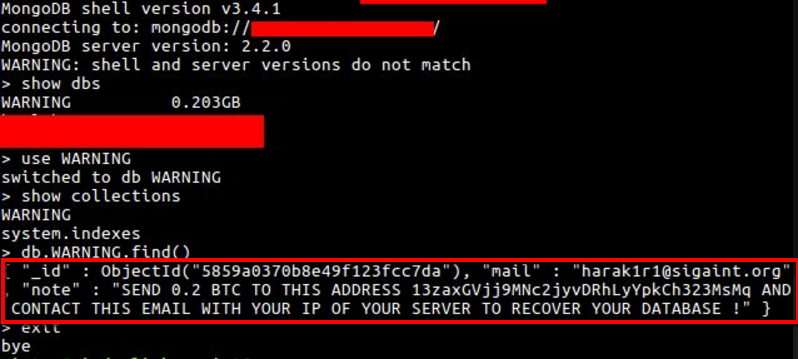
Figure 2: Example of a database corruption ransomware attack against MongoDB
Backup encryption or complete wipeout: Backups are important to have as a mitigation technique against ransomware. However, relying on backups isn’t ideal—primarily because a lot of time is required to get systems back up and running (they obviously don’t serve as a prevention mechanism). This downtime can be costly for employees and customers—the case of ransomware locking up San Francisco public transportation ticket machines is yet another example (see Image 1).
Still, backups are one of a few possible mitigation options after a ransomware attack has already struck. Subsequently, it’s possible that we’ll see ransomware targeting backups to maximize the chances of getting paid.

Image 1: When San Francisco’s public transit ticketing system was brought down by ransomware, the San Francisco Municipal Transportation Agency was forced to provide free fares for two days until the system was restored.
Data Exfiltration
Here’s where big money is still waiting to be had.
Take for example one of the latest data exfiltration attacks—Vault 7—where documentation of the CIA’s cyber weapons was leaked, then published by WikiLeaks. Ignoring the ideological agenda, let’s assume the hackers were looking for money. What do you think would have been the most profitable approach for a hacker to take with this attack…corruption or exfiltration? The possibilities include:
- Encrypting the data and demanding payment in order to decrypt it (corruption)
- Stealing the data and trying to sell it on the darkweb (exfiltration)
- Stealing the data and demanding payment in order not to disclose it (exfiltration)
Probably exfiltration. Making private data public can scare data owners the most. That’s probably why the popularity of extortionware–aka doxware– is going to rise. Exposing financial records, medical records, state-actor data, pending patents or any other sensitive data is a major threat.
If they could go back in time, do you think Netflix would have paid the ransom in order to prevent the leak of its “Orange Is the New Black” episodes? Or maybe Yahoo’s executives would have agreed to pay in order to stop the breach of one billion accounts? The actual cost of the Yahoo! breach at last count reached at least $350 million. Not that we’d endorse paying the ransom, even in these examples.
Obviously, it will never be guaranteed that paying the ransom will result with true full data disposal by the hackers (they are malicious after all), but not paying the ransom will surely end up with publishing your data or selling it to others.
While we’re seeing examples of this type of attack—demanding a ransom after your databases or files have been stolen (exfiltrated)—it’s just the tip of the iceberg. Data exfiltration has the potential to continue to be a huge money-making machine.
Disruptive, Targeted Attacks
Organizations with a large customer-base continue to be attractive candidates for attacks. The more users, the more content, the bigger financial opportunity for hackers. While attackers can plan for targeted attacks against an organization’s unique technologies, content and users, they’ll have to spend more time (and money) to conduct this type of attack.
The entry point for a disruptive, targeted attack can originate from a web vulnerability, one of the easiest ways to infect a large number of connected users or devices at once. The Internet of Things (IoT) trend only makes this type of attack more possible. Take today’s connected cars and tomorrow’s autonomous cars, both have internet connectivity, whether through an app enabling owners to control car functions, or to enable push updates to be sent from the car vendor (e.g., automatic software update).
A vulnerability in the web server communicating with the app or update mechanism can lead to remote code execution on these vehicles. For example, hackers could hold you hostage and demand a ransom, while threatening to disable your car’s brakes or steering system. The even more chaotic scenario (and bigger payout) is a hacker taking control of all of a specific vendor’s connected cars and demanding a ransom directly from the vendor.
It’s reasonable to speculate that in a few years most attacks will evolve into ransomware/extortionware, sharing this common DNA: attack by corruption, exfiltration or disruption, then demanding a ransom to stop or reverse the attack. Considering this, organizations must continue to protect their data and assets in response to these changing tactics.
How Your Organization Can Protect its Assets from Ransomware
Dealing with ransomware is not an easy task. The following guidelines will help you minimize damage and maximize the chances of preventing or repelling an attack:
- Have data audit and monitoring in place with an out-of-the box alerting system – Mainly for post-breach forensics and incident response enablement
- Enable real-time blocking – Often just alerting on an attack is too late. Real-time blocking enables attack prevention. In addition to real-time blocking, having the capability to quarantine users/hosts whose systems appear compromised provides a significant advantage.
- Use deception techniques (see Figure 3) – One of the most effective approaches when dealing with ransomware is to plant data decoys for hackers to steal/corrupt, then alert/block when that data has been accessed. Deceive the hacker and use it to your advantage.
- Perform regularly scheduled discovery and classification scans – Identify where your sensitive data is located in your network.
- Institute Insider Threat and User and Entity Behavior Analytics (UEBA) technology – Find anomalous access to your data, especially among those who already have access to it—careless, compromised or malicious insiders.
- Deploy a holistic, data-centric solution – Use a solution with one management console that centralizes protection and information about file, database, web and other ransomware attacks.
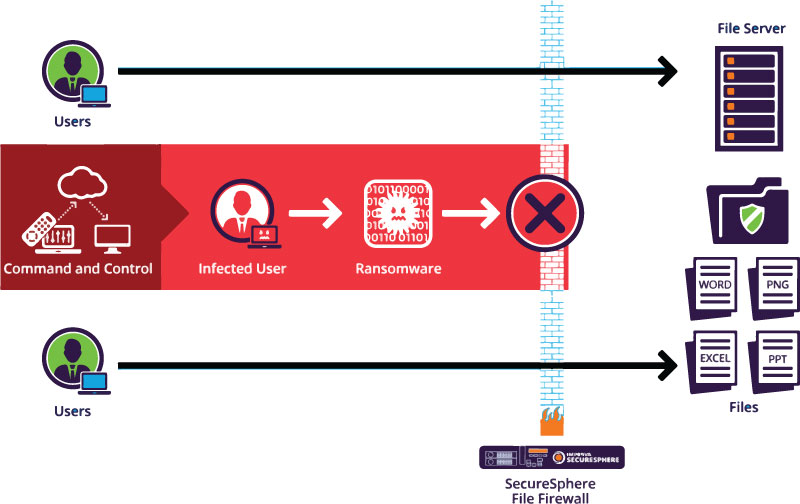
Figure 3: Uninfected users continue to access files uninterrupted while infected users are blocked from accessing a SecureSphere protected file share.
Hacker Reputation + Potential Profit = More Ransomware
Some may argue that it’s unlikely for a victim to pay the ransom when an attacker is threatening to disclose data or wipe your data, mainly because the victim has no guarantee the attackers will stand by their word and dump the sensitive data or decrypt the data or won’t attack again (attackers are malicious and untrustworthy by definition, of course).
Though in practice, we can see that attackers are getting paid.
Odd as it sounds, ransomware “vendors” do care about their reputation. They want victims to know they stand on their word – that if you do pay a ransom on time as demanded, they will stop or reverse the attack. Otherwise, their reputation is tarnished, which could potentially destroy their business model.
In conclusion, crime associated with ransomware and cyberextortion, is just getting started. The potential profit to hackers is great, and the potential risk to organizational data is even greater. It is important that enterprises take steps now to protect against these type of attacks.
Try Imperva for Free
Protect your business for 30 days on Imperva.

