What is Ransomware Attack?
Ransomware is a type of malware attack in which the attacker locks and encrypts the victim’s data, important files and then demands a payment to unlock and decrypt the data.
This type of attack takes advantage of human, system, network, and software vulnerabilities to infect the victim’s device—which can be a computer, printer, smartphone, wearable, point-of-sale (POS) terminal, or other endpoint.
Ransomware Attack Examples
There are thousands of strains of ransomware malware. Below we list a few malware examples that made a global impact and caused widespread damage.
WannaCry
WannaCry is an entrypting ransomware that exploits a vulnerability in the Windows SMB protocol, and has a self-propagation mechanism that lets it infect other machines. WannaCry is packaged as a dropper, a self-contained program that extracts the encryption/decryption application, files containing encryption keys, and the Tor communication program. It is not obfuscated and relatively easy to detect and remove. In 2017 WannaCry spread rapidly across 150 countries, affecting 230,000 computers and causing an estimated $4 billion in damages.
Cerber
Cerber is ransomware-as-a-service (RaaS), and is available for use by cybercriminals, who carry out attacks and spread their loot with the malware developer. Cerber runs silently while it is encrypting files, and may try to prevent antivirus and Windows security features from running, to prevent users from restoring the system. When it successfully encrypts files on the machine, it displays a ransom note on the desktop wallpaper.
Locky
Locky is able to encrypt 160 file types, primarily files used by designers, engineers and testers. It was first released in 2016. It is primarily distributed by exploit kits or phishing—attackers send emails that encourage the user to open a Microsoft Office Word or Excel file with malicious macros, or a ZIP file that installs the malware upon extraction.
Cryptolocker
Cryptolocker was released in 2017, and affected over 500,000 computers. It typically infects computers through email, file sharing sites, and unprotected downloads. It not only encrypts files on the local machine, but can also scan mapped network drives, and encrypt files it has permission to write to. New variants of Crypolocker are able to elude legacy antivirus software and firewalls.
NotPetya and Petya
Petya is ransomware that infects a machine and encrypts an entire hard drive, by accessing the Master File Table (MFT). This makes the entire disk inaccessible, although the actual files are not encrypted. Petya was first seen in 2016, and was spread mainly through a fake job application message linking to an infected file stored in Dropbox. It only affected Windows computers.
Petya requires the user to agree to give it permission to make admin-level changes. After the user agrees, it reboots the computer, shows a fake system crash screen, while it starts encrypting the disk behind the scenes. It then shows the ransom notice.
The original Petya virus was not highly successful, but a new variant, named NotPetya by Kaspersky Labs, proved to be more dangerous. NotPetya is equipped with a propagation mechanism, and is able to spread without human intervention.
NotPetya originally spread using a backdoor in accounting software used widely in the Ukraine, and later used EternalBlue and EternalRomance, vulnerabilities in the Windows SMB protocol. NotPetya not only encrypts the MFT but also other files on the hard drive. While encrypting the data, it damages it in such a way that it cannot be recovered. Users who pay the ransom cannot actually get their data back.
Ryuk
Ryuk infects machines via phishing emails or drive-by downloads. It uses a dropper, which extracts a trojan on the victim’s machine and establishes a persistent network connection. Attackers can then use Ryuk as a basis for an Advanced Persistent Threat (APT), installing additional tools like keyloggers, performing privilege escalation and lateral movement. Ryuk is installed on each additional system the attackers gain access to.
Once the attackers have installed the trojan on as many machines as possible, they activate the locker ransomware and encrypt the files. In a Ryuk-based attack campaign, the ransomware aspect is only the last stage of the attack, after the attackers have already done damage and stolen the files they need.
GrandCrab
GrandCrab was released in 2018. It encrypts files on a user’s machine and demands a ransom, and was used to launch ransomware-based extortion attacks, where attackers threatened to reveal victims’ porn-watching habits. There are several versions, all of which target Windows machines. Free decryptors are available today for most versions of GrandCrab.
Ransomware Distribution Techniques
The device is infected when the victim clicks a link, visits a web page, or installs a file, application, or program that includes malicious code designed to covertly download and install the ransomware. This can happen in a variety of ways:
| Distribution Techniques | Description |
| Phishing email | Clicking a link embedded in an email, which redirects to a malicious web page. |
| Email attachments | Opening an email attachment and enabling malicious macros; or downloading a document embedded with a Remote Access Trojan (RAT); or downloading a ZIP file containing a malicious JavaScript or Windows Script Host (WSH) file. |
| Social media | Clicking a malicious link on Facebook, Twitter, social media posts, instant messenger chats, etc. |
| Malvertising | Clicking a legitimate advertising site seeded with malicious code. |
| Infected programs | Installing an application or program containing malicious code. |
| Drive-by infections | Visiting an unsafe, suspicious, or fake web page; or opening or closing a pop-up.NOTE: A legitimate web page can be compromised if a malicious JavaScript code is injected into the page’s content. |
| Traffic Distribution System (TDS) | Clicking a link on a legitimate gateway web page that redirects the user to a malicious site, based on the user’s geo-location, browser, operating system, or other filter. |
| Self-propagation | Spreading the malicious code to other devices through network and USB drives. |
How Does Ransomware Work?
After a device is exposed to the malicious code, the ransomware attack proceeds as follows. Ransomware can remain dormant on a device until the device is at its most vulnerable, and only then execute an attack.
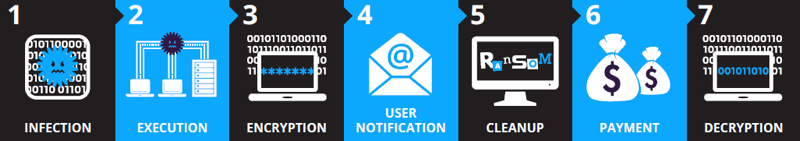
Ransomware seven-stage attack
- Infection—Ransomware is covertly downloaded and installed on the device.
- Execution—Ransomware scans and maps locations for targeted file types, including locally stored files, and mapped and unmapped network-accessible systems. Some ransomware attacks also delete or encrypt any backup files and folders.
- Encryption—Ransomware performs a key exchange with the Command and Control Server, using the encryption key to scramble all files discovered during the Execution step. It also locks access to the data. (See Figure 2.)
- User Notification—Ransomware adds instruction files detailing the pay-for-decryption process, then uses those files to display a ransom note to the user.
- Cleanup—Ransomware usually terminates and deletes itself, leaving only the payment instruction files.
- Payment—Victim clicks a link in the payment instructions, which takes the victim to a web page with additional information on how to make the required ransom payment. Hidden TOR services are often used to encapsulate and obfuscate these communications to avoid detection by network traffic monitoring.
- Decryption—After the victim pays the ransom, usually via the attacker’s Bitcoin address, the victim may receive the decryption key. However, there is no guarantee the decryption key will be delivered as promised.
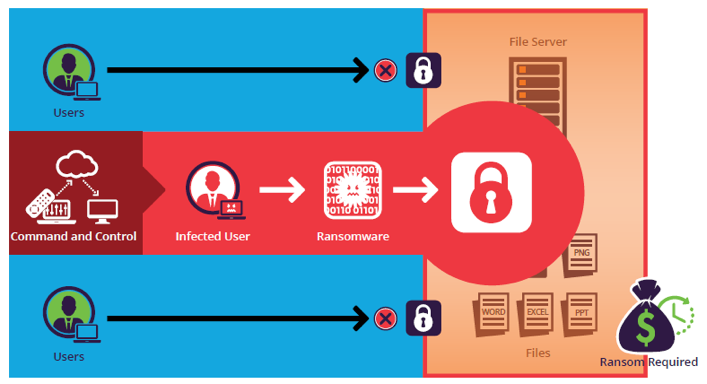
One infected user can result in a data lockout for all users
Ransomware Protection
Here are several best practices that can help you prevent and protect against Ransomware infections in your organization:
Endpoint Protection
Antivirus is an obvious first step in ransomware protection, but legacy antivirus tools can only protect against some ransomware variants.
Modern endpoint protection platforms provide next-generation antivirus (NGAV), which protects against evasive or obfuscated ransomware, fileless attacks like WannaCry, or zero-day malware whose signature is not yet found in malware databases. They also offer device firewalls and Endpoint Detection and Response (EDR) capabilities, which help security teams detect and block attacks occurring on endpoints in real time.
Data Backup
Regularly backup data to an external hard-drive, using versioning control and the 3-2-1 rule (create three backup copies on two different media with one backup stored in a separate location). If possible, disconnect the hard-drive from the device to prevent encryption of the backup data.
Patch Management
Keep the device’s operating system and installed applications up-to-date, and install security patches. Run vulnerability scans to identify known vulnerabilities and remediate them quickly.
Application Whitelisting and Control
Establish device controls that allow you to limit applications installed on the device to a centrally-controlled whitelist. Increase browser security settings, disable Adobe Flash and other vulnerable browser plugins, and use web filtering to prevent users from visiting malicious sites. Disable macros on word processing and other vulnerable applications.
Email Protection
Train employees to recognize social engineering emails, and conduct drills to test if employees are able to identify and avoid phishing. Use spam protection and endpoint protection technology to automatically block suspicious emails, and block malicious links if user does end up clicking on them.
Network Defenses
Use a firewall or web application firewall (WAF), Intrusion Prevention / Intrusion Detection Systems (IPS/IDS), and other controls to prevent ransomware from communicating with Command & Control centers.
Ransomware Detection
Use real-time alerting and blocking to automate identifying ransomware-specific read/write behavior and then blocking users and endpoints from further data access.
Use deception-based detection, which strategically plants hidden files on file storage systems to identify ransomware encryption behaviors at the earliest attack stage. Any write/rename actions on the hidden files automatically triggers a block of the infected user or endpoint, while continuing to allow access by uninfected users and devices.
Use granular reporting and analysis to provide detailed audit trail support for forensic investigations into who, what, when, where, and how users access files.
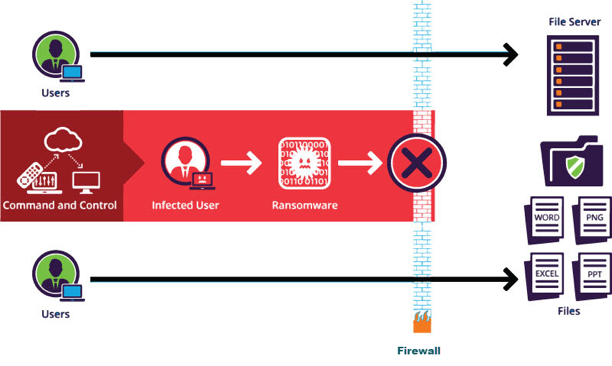
Deception-based detection measure ensures that only the infected user is blocked from accessing data
Ransomware Removal: How to Mitigate an Active Ransomware Infection
If you detected a Ransomware infection in your network, here are the immediate steps you should take to mitigate the ransomware threat:
- Isolate – identify infected machines, disconnect from networks and lock shared drives to prevent encryption.
- Investigate – see what backups are available for encrypted data. Check what strain on ransomware you were hit with, and if there are decryptors available. Understand if paying the ransom is a viable option.
- Recover – if no decryptor tools are available, restore your data from backup. In most countries, the authorities do not recommend paying the ransom, but this may be a viable option in some extreme cases. Use standard practices to remove ransomware or wipe and reimage affected systems.
- Reinforce – run a lessons learned session to understand how internal systems were infected and how to prevent a recurrence. Identify the key vulnerabilities or lacking security practices that allowed the attackers in, and remediate them.
- Evaluation – once the crisis has passed, it’s important to evaluate what happened and the lessons learned. How was ransomware successfully executed? Which vulnerabilities made penetration possible? Why did antivirus or email filtering fail? How far did the infection spread? Was it possible to wipe and reinstall infected machines, and were you able to successfully restore from backup? Address the weak points in your security posture to be better prepared for the next attack.
Imperva Data Protection Solutions
Imperva File Security can detect ransomware activity before it does widespread damage, using policy-based monitoring and deception technology. Imperva identifies suspicious file access behavior in real time, and quarantines infected users or devices which may be affected by ransomware. It also provides data that can help security teams investigate and report on ransomware activity.
In addition, Imperva protects against server-side ransomware attacks, with the industry’s leading web application firewall (WAF), which can detect and block ransomware when it attempts to contact its Command & Control center.
In addition to ransomware detection and prevention, Imperva’s data security solution protects your data wherever it lives—on premises, in the cloud and in hybrid environments. It also provides cyber security and IT teams with full visibility into how the data is being accessed, used, and moved around the organization.
Our comprehensive approach relies on multiple layers of protection, including:
- Database firewall—blocks SQL injection and other threats, while evaluating for known vulnerabilities.
- Data masking and encryption—obfuscates sensitive data so it would be useless to the bad actor, even if somehow extracted.
- Data loss prevention (DLP)—inspects data in motion, at rest on servers, in cloud storage, or on endpoint devices.
- User behavior analytics—establishes baselines of data access behavior, uses machine learning to detect and alert on abnormal and potentially risky activity.
- Data discovery and classification—reveals the location, volume, and context of data on premises and in the cloud.
- Database activity monitoring—monitors relational databases, data warehouses, big data and mainframes to generate real-time alerts on policy violations.
- Alert prioritization—Imperva uses AI and machine learning technology to look across the stream of security events and prioritize the ones that matter most.