What is File Integrity Monitoring (FIM)?
The term FIM refers to IT security technologies and processes used to check whether certain components were corrupted or tampered with. You can use FIM to inspect operating systems (OS), databases, and application software files.
A FIM solution establishes a trusted, known baseline for each file, and performs audits of all changes to files, by comparing them to this baseline. If it determines that a file has been tampered with, updated, or corrupted, it generates an alert to enable further investigation and action.
You can use FIM in two ways:
- Active monitoring—live monitoring of changes to files based on rules or behavioral analysis
- Reactive auditing—forensic examination of files after security incidents
How File Security Enables File Integrity Monitoring
File Integrity Monitoring solutions rely on file security features built into modern operating systems and databases.
Windows file security
In Windows, files are securable objects. Access is managed by the same access control model that manages all other securable Windows objects.
Windows compares the permissions and information requested by the thread access token with the information in the security descriptor of the file or directory. If there is a match, a handle is returned to the thread and authorization is granted.
Linux file security
The Linux security model is based on the robust security model used by UNIX systems. In Linux, there are three categories of users: owner, group, and other users. The owner can grant or deny read, write, and execute permissions for each user category.
Linux returns one of four access codes when access is requested to a file:
- 0—access not granted to the user category
- 4—read access only granted to the user category
- 2—write access granted to the user category
- 1—execute permission granted to the user category
Database file security
All modern databases have built-in file security features. For example, an Oracle database has the same user categories as Linux—owner, group, and other users. Only the owner of the file or root can assign or modify file permissions. Permissions include read, write, execute, and denied—meaning users do not have any access to the file.
Why is File Integrity Monitoring Important?
File integrity monitoring software tracks, analyzes, and reports about unexpected changes to critical files in your IT environment. It can support incident response while providing an important layer of file security for data stores and applications. The four main use cases for monitoring file integrity are:
- Detecting malicious activity—when security breaches occur, it is important to know whether they have attempted to modify important files in operating systems or applications on your IT systems. Even if log files and other detection systems are bypassed or changed, FIM can detect changes to key parts of the IT ecosystem.
- Identifying accidental changes—it is quite common for an employee or other authorized party to accidentally modify or delete a file. In some cases, a change can hurt the stability of a system, create a security backdoor, or result in loss or corruption of sensitive data. Monitoring file integrity simplifies forensic investigations by showing what happened, where, and by whom.
- Verifying updates and system integrity—IT systems are often updated. You can use FIM solutions to run scans on multiple systems that had the same patch applied, to ensure that they are all updated correctly, by comparing their file checksum. Similarly, you can scan multiple systems using the same OS or software, to ensure all systems are running a consistent version of the software.
- Compliance—standards like SOX, HIPAA, and PCI DSS mandate that an organization should monitor and report on changes to files. See the regulations that require FIM in the section below.
How File Integrity Monitoring Software Works
File integrity monitoring solutions typically have four key components:
- Database—stores information about the original state and settings of files in an encrypted hash format.
- Agents—deployed on computers FIM needs to monitor, collect data from hardware and applications and store it in the database
- Analysis engine—FIM systems analyze file data to identify important changes, based on static rules and/or behavioral analysis based on machine learning algorithms
- User interface—a user interface that enables FIM administrators to access reports, actively search for file changes, and configure alerts.
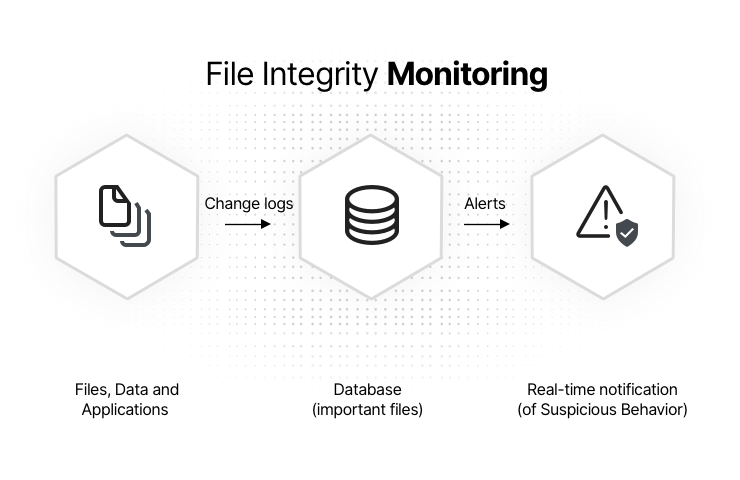
How file integrity monitoring works
5 Steps to Implementing a File Integrity Monitoring Solution
You can follow the process below to prepare your organization for a FIM solution, and implement it effectively.
1. Defining a policy
A FIM strategy begins with policies. In this step, the company determines which files it needs to monitor, what kinds of changes can have an impact, and who should be notified and take action.
2. Setting baselines for files
Based on the policies, a FIM solution scans the relevant files across the organization and sets a baseline of “known good” files. Some compliance standards require this baseline to be documented in a way that can be presented to an auditor.
The baseline typically includes the version, creation/modification date, a checksum, and other information that IT experts can use to verify that the file is valid.
3. Monitoring
Once the baseline is recorded across all relevant files, FIM can continuously monitor all files for changes. Because files are often changed legitimately, FIM can generate a large number of false positives—alerting about a change to a file even though it is not malicious or impactful.
A FIM system can use several strategies to avoid false positives. Administrators can define (in advance or after receiving a false positive alert) rules indicating which types of changes are expected or allowed. A FIM system can also use behavioral analysis to determine if the change is “normal” or constitutes an “anomaly” that needs to be investigated.
4. Sending alerts
When a file integrity monitoring solution detects significant, unauthorized changes, a file security alert should be sent to the teams or individuals who are responsible for that data or system, and are responsible for investigating the problem. FIMs may send alerts to IT staff, database or file server administrators, or security teams.
5. Reporting results
A FIM generates period reports showing file activity and changes in the organization. These reports might be used internally by security or IT staff. Or they can be delivered to auditors for compliance purposes (see the following section).
Compliance Standards that Require File Integrity Checks
FIM solutions are commonly used to comply with regulations or compliance standards. Below are the file security requirements of several common compliance standards with regard to file security.
PCI DSS
The Payment Card Industry Data Security Standard (PCI DSS) regulates the security activities of organizations involved in processing payment cards. There are two parts of the PCI standard that specifically describe the requirements for file integrity monitoring:
- 10.5.5—use file integrity monitoring or change detection software to ensure any change to log data triggers an alert
- 11.5—implement change detection monitoring to compare critical system, content or configuration files, and generate alerts about any unauthorized changes.
SOX
The Sarbanes Oxley Act (SOX) is a federal law that establishes accountability requirements for the board of directors of US publicly traded companies, their management and their accounting firms.
SOX does not specify the specific methods an organization should use to meet its requirements. Most organizations rely on the COBIT framework for regulatory compliance. COBIT has 34 control objectives organized into four groups. Here are the groups and specific objectives relevant for file integrity monitoring:
“Build, Acquire and Implement (BAI)
- BAI06—Manage Changes
- BAI09—Manage Assets
- BAI10—Manage Configuration
Deliver, Service and Support (DSS)
- DSS03—Manage Problems
- DSS04—Manage Continuity
- DSS06—Manage Business Process Controls
Monitor, Evaluate and Assess (MEA)
- MEA01—Monitor, Evaluate and Assess Performance and Conformance
- MEA02—Monitor, Evaluate and Assess Internal Control”
GDPR
The General Data Protection Regulation (GDPR) applies to all companies that process personal data of EU data subjects. You can use FIM to meet the following GDPR requirements:
- Article 25—data protection by design and data protection by default
- Article 32—security for data processing
- Article 39—duties of the Data Protection Officer (DPO)
- Article 57—tasks performed by supervisory authority (including audits and complaints)
- Article 59—activity reports
HIPAA
The Health Insurance Portability and Accountability Act of 1996 (HIPAA) includes safeguards to ensure the integrity, availability, and confidentiality of protected medical information.
The HIPAA Security Rule refers to five technical controls that may be related to file security: introduction, authentication, protection, technical safeguards, and data integrity protection.
In addition, according to NIST Special Publication 800-66, a FIM solution can help achieve the requirement for “continuous evaluation of access controls and data security”, which is specified in HIPAA best practices.
File Security with Imperva
Organizations that leverage file integrity monitoring to protect their sensitive data are in need of a holistic security solution. Even with FIM technology in place, infrastructure and data sources like databases need to be protected from increasingly sophisticated attacks.
Imperva protects data stores to ensure compliance and preserve the agility and cost benefits you get from your cloud investments:
Cloud Data Security – Simplify securing your cloud databases to catch up and keep up with DevOps. Imperva’s solution enables cloud-managed services users to rapidly gain visibility and control of cloud data.
Database Security – Imperva delivers analytics, protection and response across your data assets, on-premise and in the cloud – giving you the risk visibility to prevent data breaches and avoid compliance incidents. Integrate with any database to gain instant visibility, implement universal policies, and speed time to value.
Data Risk Analysis – Automate the detection of non-compliant, risky, or malicious data access behavior across all of your databases enterprise-wide to accelerate remediation.