Data Security
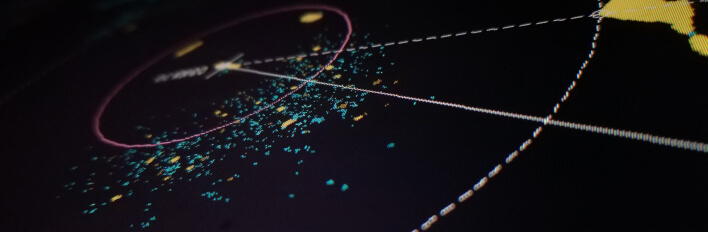
Identify risks and manage compliance for all your global data repositories, through Imperva’s Data Security Fabric that is designed to work anywhere your data is located.
Where is my data, and what are users or computer systems doing with it? Constantly growing data stores, and increasingly fragmented technology ecosystems, have made this an impossible question for security teams to answer.

Imperva named an overall leader in the 2023 KuppingerCole Leadership Compass for Data Security Platforms
The most complete platform support for cloud, multi-cloud, on-premises, and hybrid database environments
Trusted organizations rely on Imperva for all their data security needs
“Out-of-the-box”, pre-configured, and extensible templates, policies, reports, and more are available to you, for quick, continuous compliance and risk management
More from the blogConsolidated visibility across globally distributed environments (on-premises, in the cloud, multi-cloud and hybrid) to discover ungoverned data repositories, classify data, assess vulnerabilities, and investigate suspicious user activities
More from the blogDetect both external attacks and insider threats and automate response procedures
More from the blogConsolidate reporting operations and get cost effective multi-year retention of audit and forensic records
More from the blogThe Imperva Data Security Fabric (DSF) is a data risk manager that provides you with the visibility of your data, analytics, reporting, event alerting, and automation needed to perform proactive responses to compliance and data security objectives.
Account compromise / Credential highjacking
Account abuse or misuse
Brute force attacks
Code injection
Insider and outsider (external) threats
Entitlement reviews
Report sign offs
Change control processes
Sensitive data event alerts
Global database discovery
Contextual metadata
Vulnerability management history
User entitlement summaries
Classified data types
Identify risks and manage compliance for all your global data repositories, through Imperva’s Data Security Fabric that is designed to work anywhere your data is located.
Continuously discover and classify all your valuable data whether it’s structured or unstructured, and located on-premises, hybrid, cloud, or multi-cloud environments.
100% visibility into your AWS and Azure cloud or multi-cloud) databases, with 0% hassle. Imperva enables complete AWS, Azure, and multi-cloud database security.