What Is Identity and Access Management
An Identity and Access Management (IAM) system defines and manages user identities and access permissions. Users of IAM include customers (customer identity management) and employees (employee identity management). With IAM technologies, IT managers can ensure that users are who they say they are (authentication) and that users access the applications and resources they have permission to use (authorization).
4 Key Benefits of Identity and Access Management Systems
- Eliminating weak passwords—research shows over 80% of data breaches are caused by stolen, default, or weak passwords. IAM systems enforce best practices in credential management, and can practically eliminate the risk that users will use weak or default passwords. They also ensure users frequently change passwords.
- Mitigating insider threats—a growing number of breaches is caused by insiders. IAM can limit the damage caused by malicious insiders, by ensuring users only have access to the systems they work with, and cannot escalate privileges without supervision.
- Advanced tracking of anomalies—modern IAM solutions go beyond simple credential management, and include technologies such as machine learning, artificial intelligence, and risk-based authentication, to identify and block anomalous activity.
- Multi-factor security—IAM solutions help enterprises progress from two-factor to three-factor authentication, using capabilities like iris scanning, fingerprint sensors, and face recognition.
Top 5 Benefits of Identity and Access Management
Improved security
IAM solutions help identify and mitigate security risks. You can use IAM to identify policy violations or remove inappropriate access privileges, without having to search through multiple distributed systems. You can also leverage IAM to ensure that security measures are in place to meet regulatory and audit requirements.
Information sharing
IAM provides a common platform for access and identity management information. You can apply the same security pollies across all the operating platforms and devices used by the organization. IAM frameworks can help you enforce policies related to user authentication, privileges, and validation, and attend to “privilege creep”.
Ease of use
IAM simplifies signup, sign-in and user management processes for application owners, end-users and system administrators. IAM makes it simple to provide and manage access, and this promotes user satisfaction.
Productivity gains
IAM centralizes and automates the identity and access management lifecycle, creating automated workflows for scenarios like a new hire or a role transition. This can improve processing time for access and identity changes and reduce errors.
Reduced IT Costs
IAM services can lower operating costs. Using federated identity services means you no longer need local identities for external uses; this makes application administration easier. Cloud-based IAM services can reduce the need to buy and maintain on-premise infrastructure.
What IAM Means for Compliance Management
If identity access management processes are not effectively controlled, you may be in noncompliance with industry standards or government regulations. Also, if your organization is audited, you may not be able to show that company data is protected against misuse.
IAM systems are instrumental in compliance efforts. It can provide many of the safety controls required by security standards and can demonstrate to auditors that corporate information is appropriately controlled.
IAM and Directory Services in the Cloud
Traditionally, IAM solutions relied on local directory services, often based on Microsoft Active Directory or OpenLDAP. Actual user credentials were stored in an on-premises directory.
Today, the control model is changing, and organizations are adopting pure cloud-based identity solutions – both the directory service and the IAM management layer are hosted in the cloud. Cloud-based directory services, known as Directory as a Service (DaaS), have the following benefits:
- Accessible from anywhere—authenticate and authorize no matter where your users or employees are located.
- Central directory service—a cloud-based core directory service can be a single directory service for your entire organization or even multiple organizations.
- Broad support for devices and applications—DaaS solutions are infrastructure-agnostic and can support machines with Mac, Windows or Linux operating systems, cloud servers hosted on AWS or Azure, SaaS-based applications and on-premise applications.
- Improved security—without a central DaaS solution, you may need to re-create directory services for cloud systems or SaaS applications. DaaS provides central control over all IT assets and can add security layers like multi-factor access, strong passwords, and SSH keys.
- No upfront investment—DaaS is typically offered with on-demand pricing, does not have upfront license costs and does not require maintaining a local directory server.
Imperva Data Security Solutions
Imperva’s industry-leading data security solution provides user rights management, monitoring data access, and activities of privileged users to identify excessive, inappropriate, or unused privileges. It also provides security and IT teams with full visibility into how data is being accessed, used, and moved around the organization.
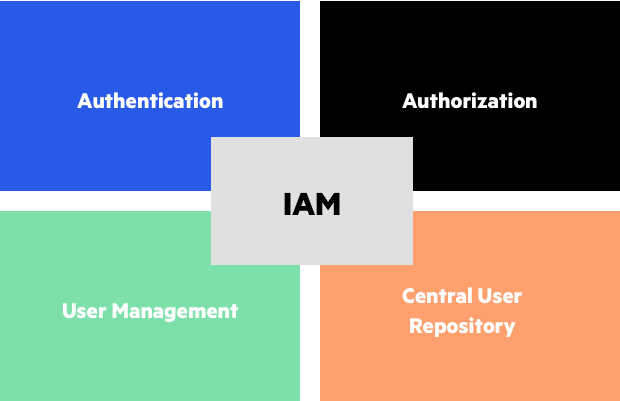
Elements of Identity and Access Management systems
Beyond user rights management, our comprehensive approach provides multiple layers of protection for enterprise data, both on-premises and in the cloud:
- Database firewall – blocks SQL injection and other threats, while evaluating for known vulnerabilities.
- Data masking and encryption – obfuscates sensitive data so it would be useless to the bad actor, even if somehow extracted.
- Data loss prevention (DLP) – inspects data in motion, at rest on servers, in cloud storage, or on endpoint devices.
- User behavior analytics – establishes baselines of data access behavior, uses machine learning to detect and alert on abnormal and potentially risky activity.
- Data discovery and classification – reveals the location, volume, and context of data on-premises and in the cloud.
- Database activity monitoring – monitors relational databases, data warehouses, big data, and mainframes to generate real-time alerts on policy violations.
- Alert prioritization – Imperva uses AI and machine learning technology to look across the stream of security events and prioritize the ones that matter most.