Ensure authentic user engagement
Mitigate bot risks effectively by managing bot-accessible content, preventing automated fraud, and eliminating fake interactions.
Advanced Bot Protection safeguards websites, mobile apps, and APIs from today’s most sophisticated bot attacks—including all OWASP 21 Automated Threats—without sacrificing customer experience and maintaining business-critical traffic flow.
Multi-layered detection stops the most sophisticated automated threats with the fewest false positives, combining cutting-edge techniques with human expertise. Rigorous testing and feedback loops ensure precise, reliable detection and unparalleled accuracy.
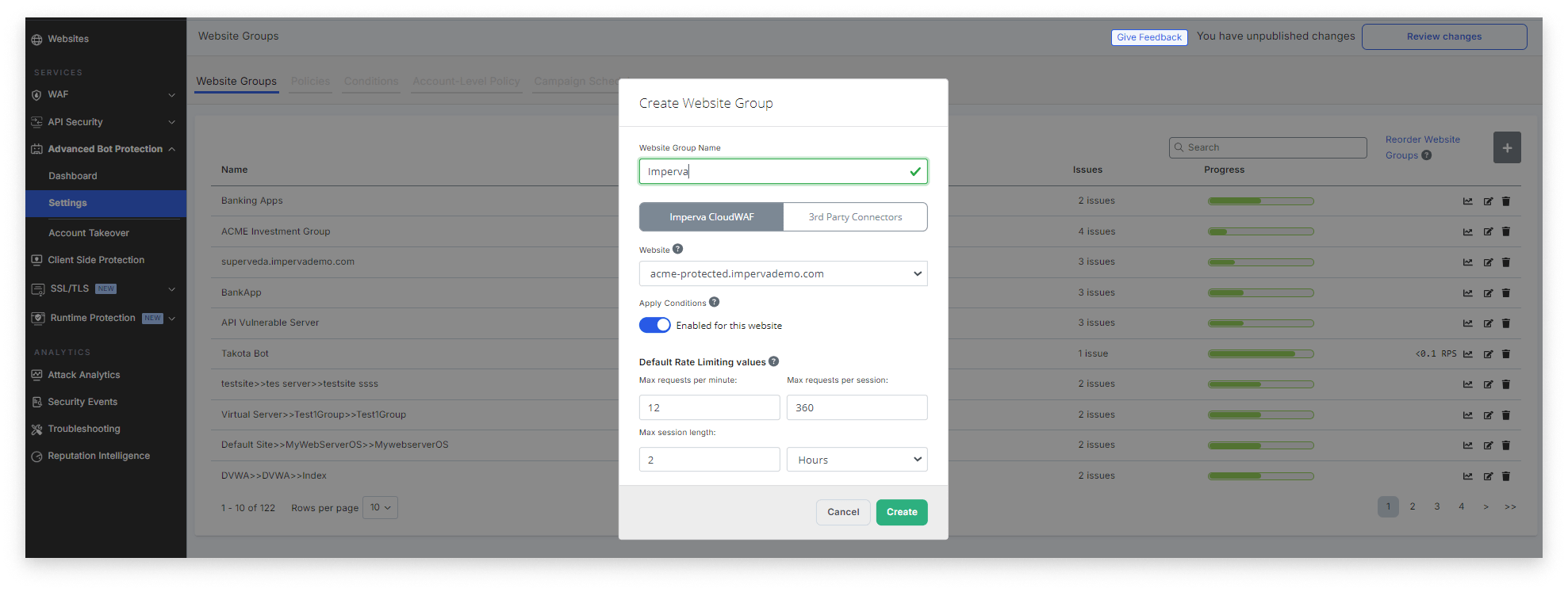
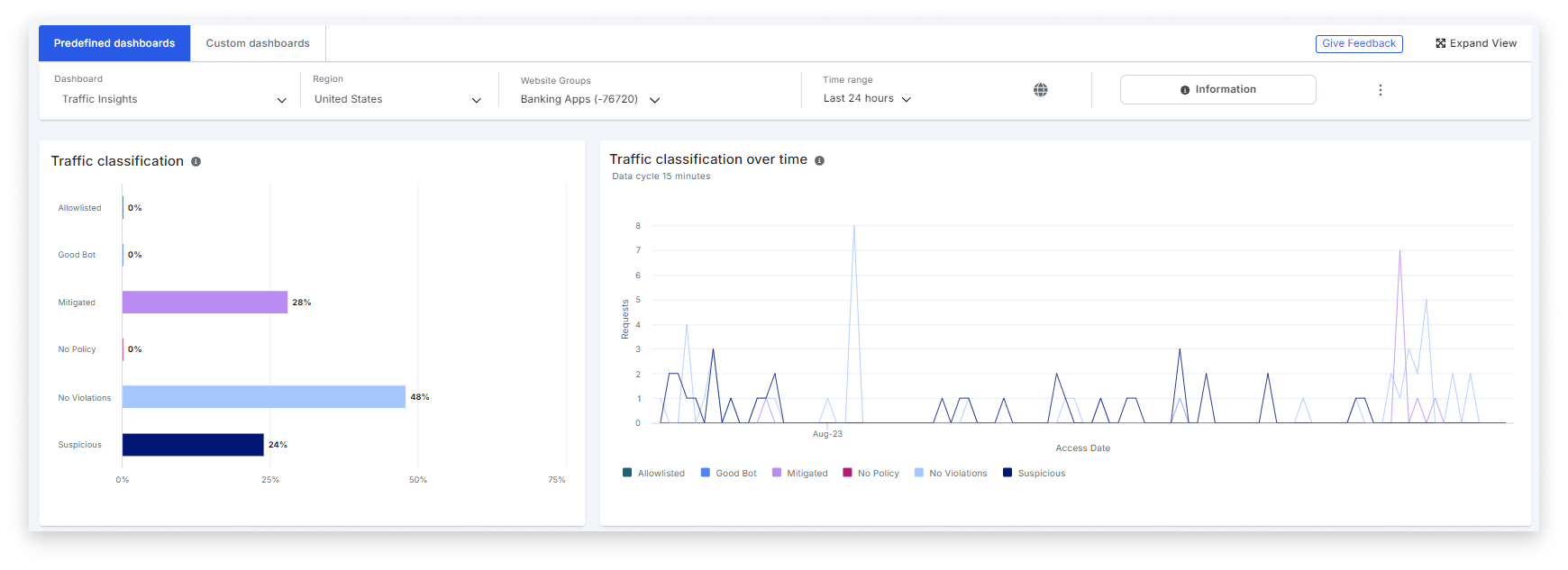
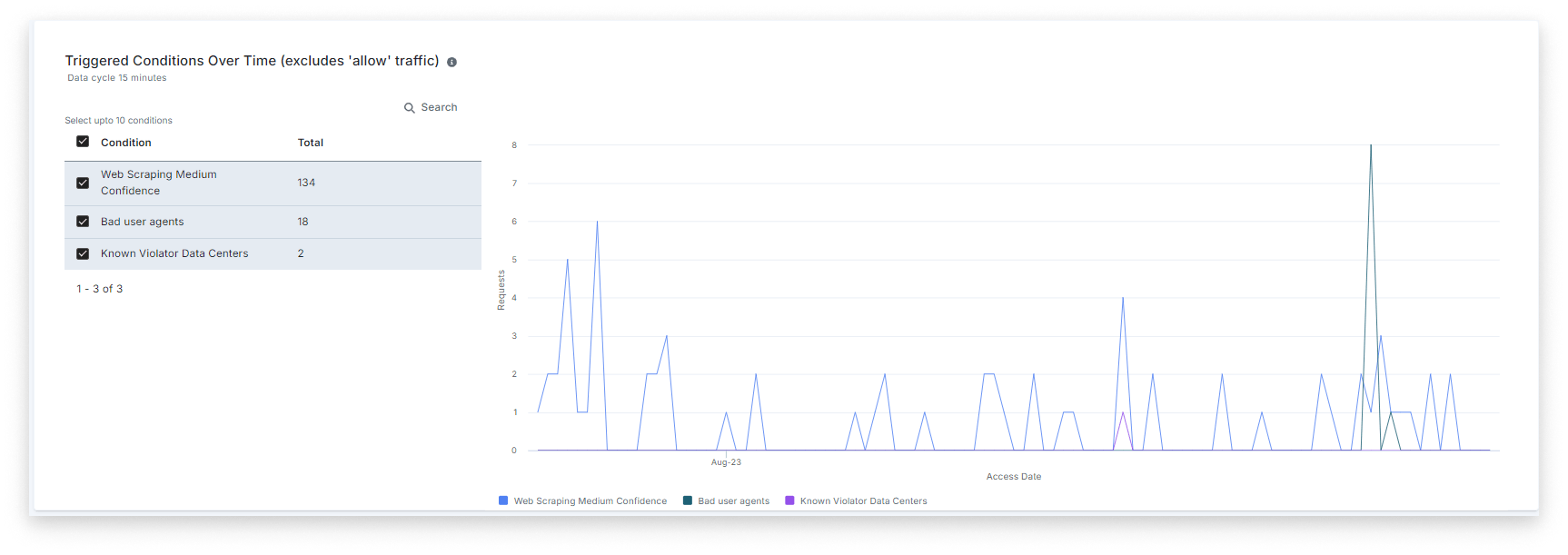
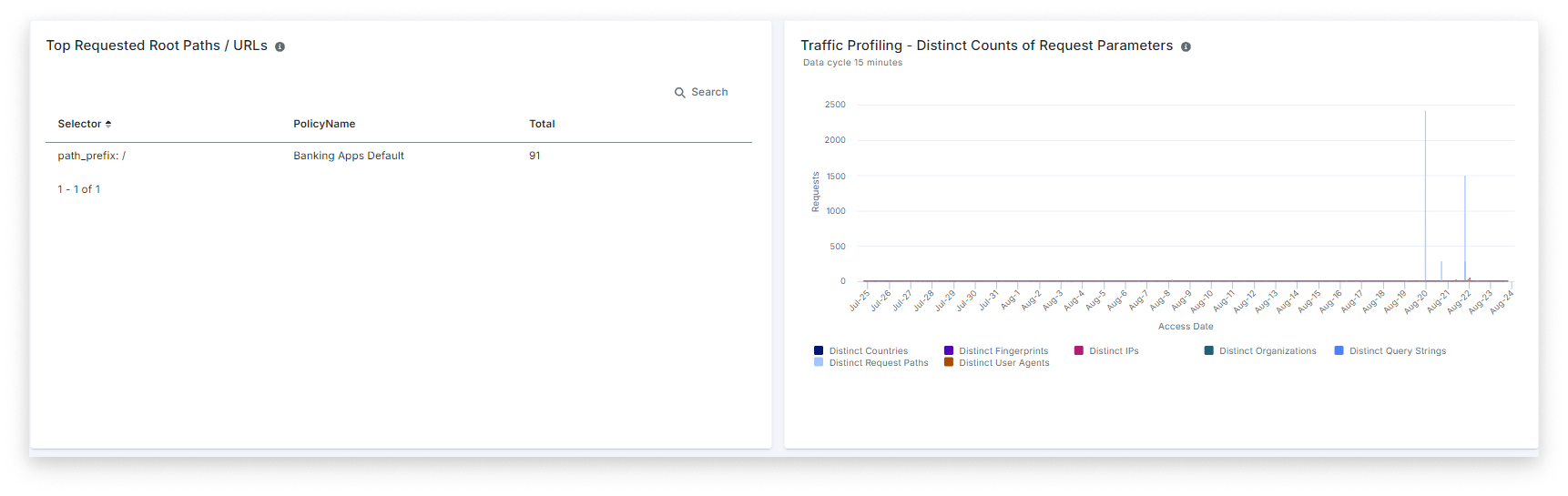
Rapidly adapt to evolving bot evasion techniques with real-time monitoring, in-depth reporting, and granular controls that enable real-time response. Explainable reporting enhances strategy optimization, false positive analysis, and policy creation.
Access to expert bot analysts with unparalleled experience combating bad bots. From the set-up process through ongoing reviews, policy fine-tuning, alerting, and more—Imperva isn’t just a vendor, but your ally in the fight against bad bots.
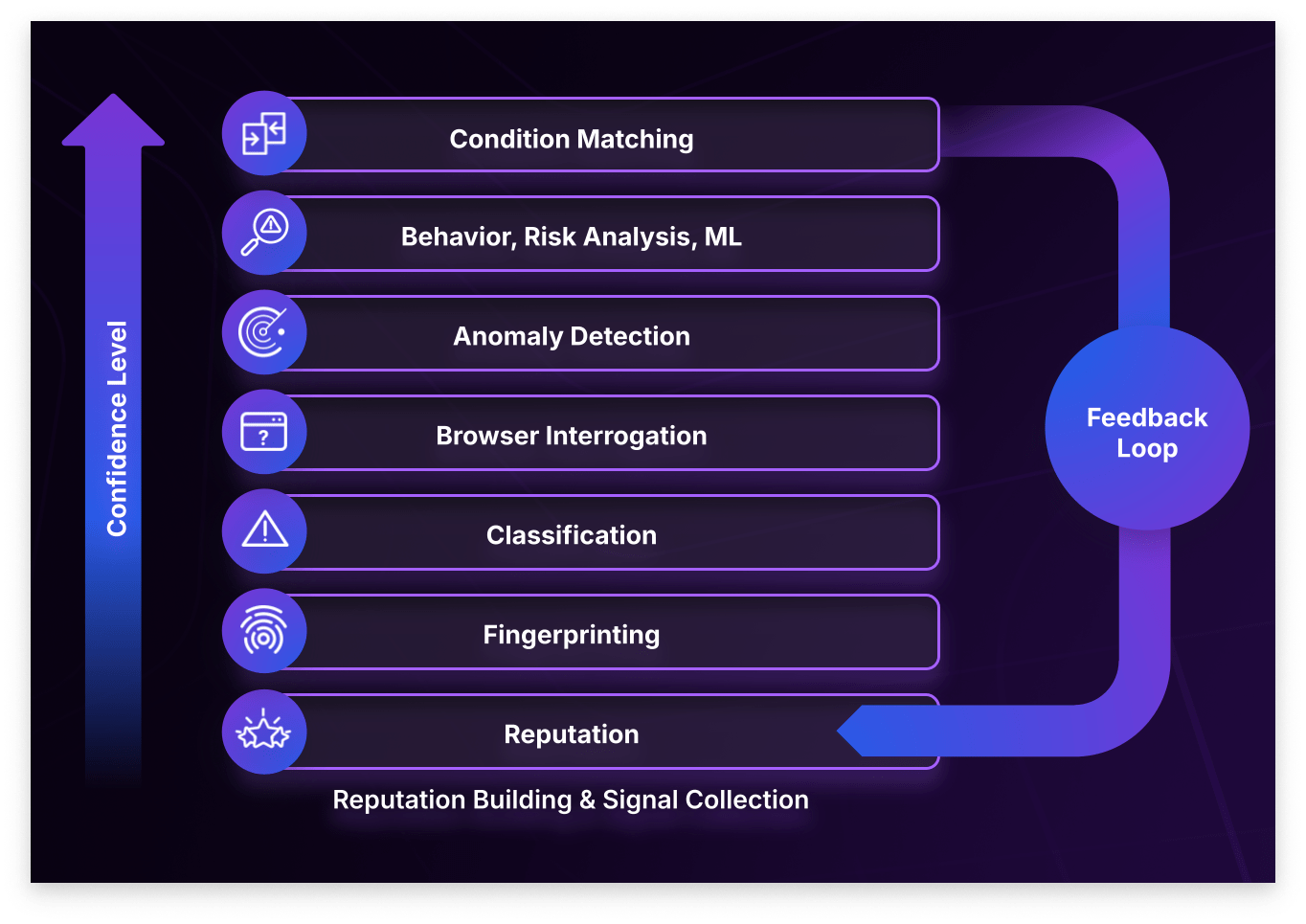
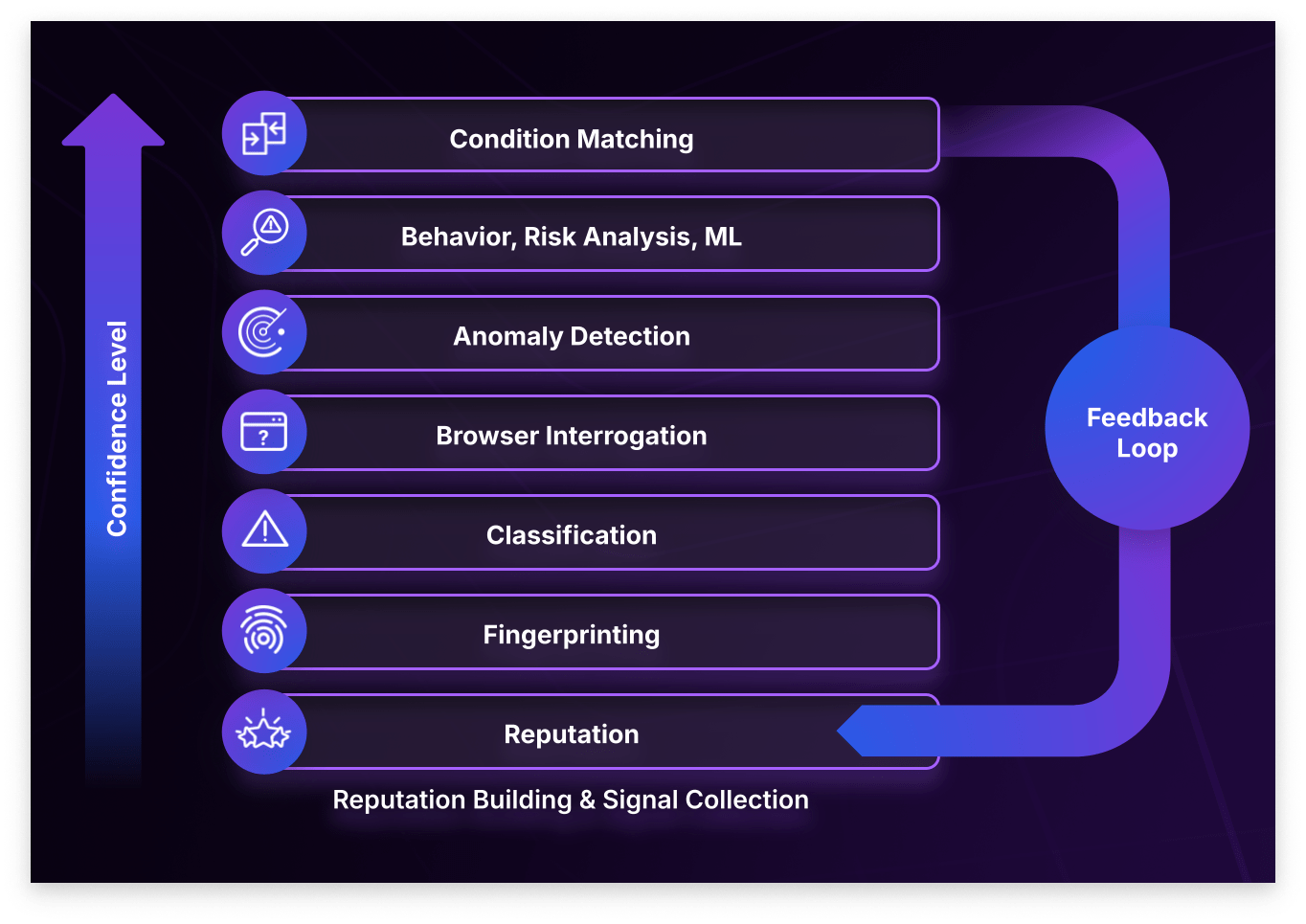
Multi-layered approach to detect malicious bots, combining direct client interrogation, behavior analysis, machine learning (ML), connection characteristics, and threat intelligence feeds. This comprehensive approach lets us detect over 700 dimensions to separate between human, good, and bad bot traffic, creating a unique fingerprint that withstands even the most sophisticated evasion techniques.
Imperva’s detection capabilities provide unparalleled precision and accuracy in identifying malicious bots. They are backed by rigorous testing and validation against historical data and hundreds of browsers to ensure accuracy. Our post-deployment feedback loops and metadata replay help minimize false positives and negatives, ensuring that our detections are consistently precise and reliable.
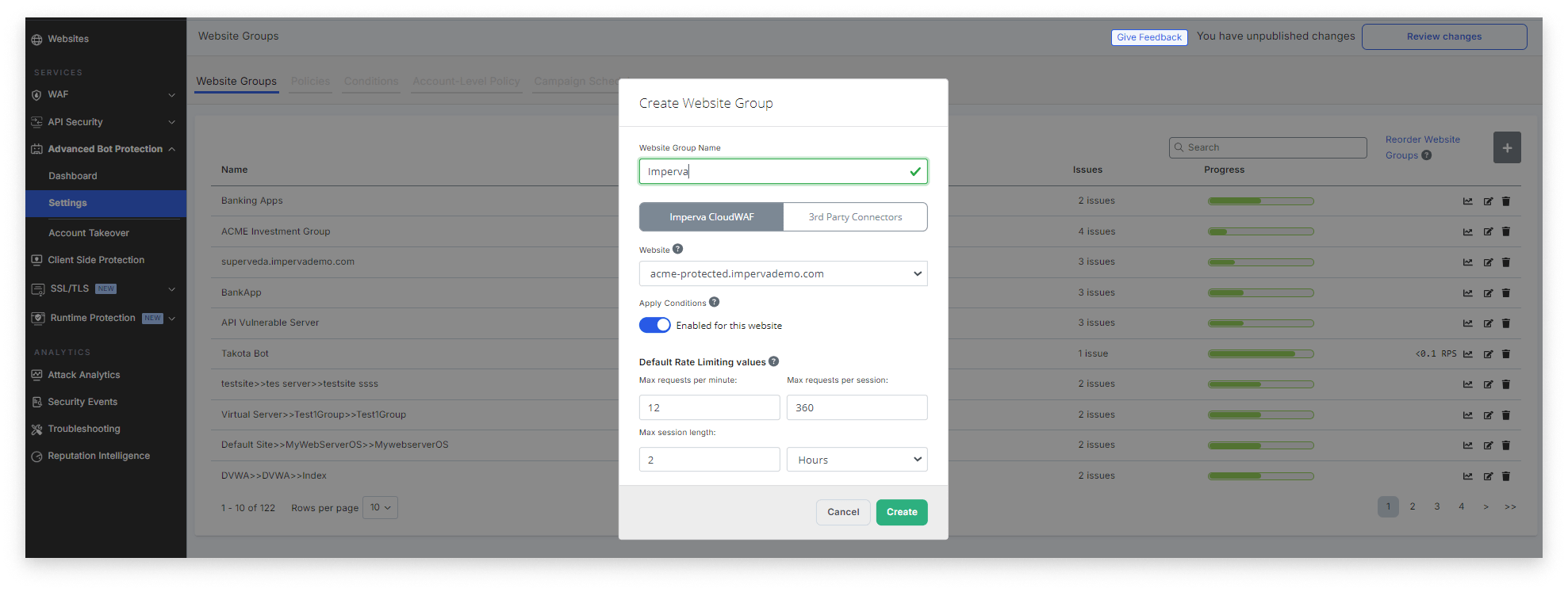
Stay ahead of evolving threats with superior adaptability that goes beyond “risk scores”. Unlike black box solutions, our platform offers full visibility and granular tuning, allowing you to customize defenses to your specific needs. This transparency ensures higher efficacy, minimizes false positives, and enhances incident response capabilities.
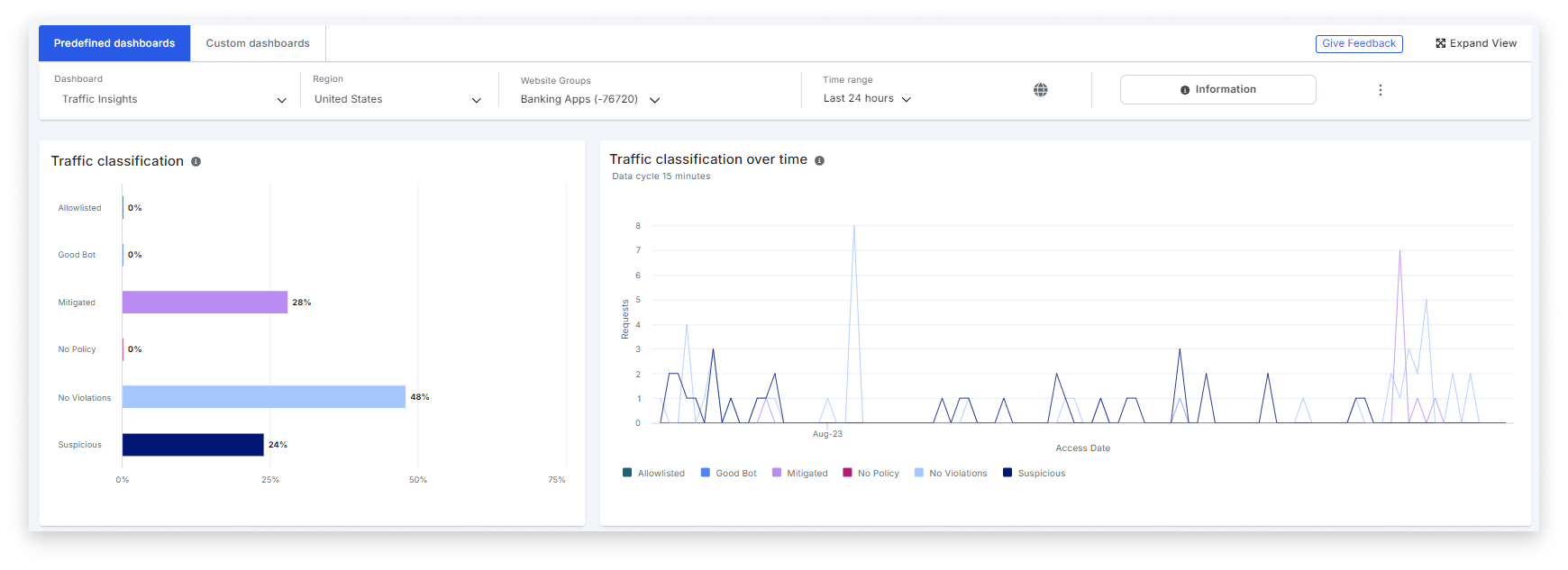
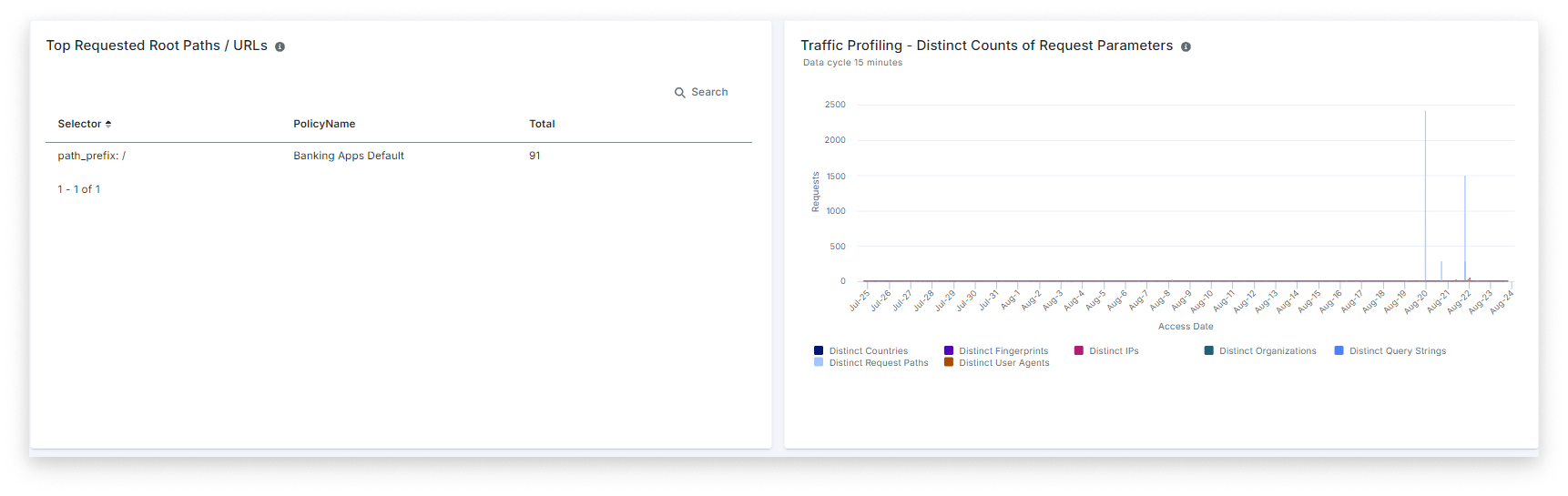
Analyze trending data across applications or in detail by path or rule. Identify targeted applications and paths, and optimize mitigation strategies. Imperva offers advanced reporting capabilities tailored to address organizations’ unique and varying needs. Leverage hundreds of unique dimensions to create customized dashboards and reports that meet your organization’s requirements.
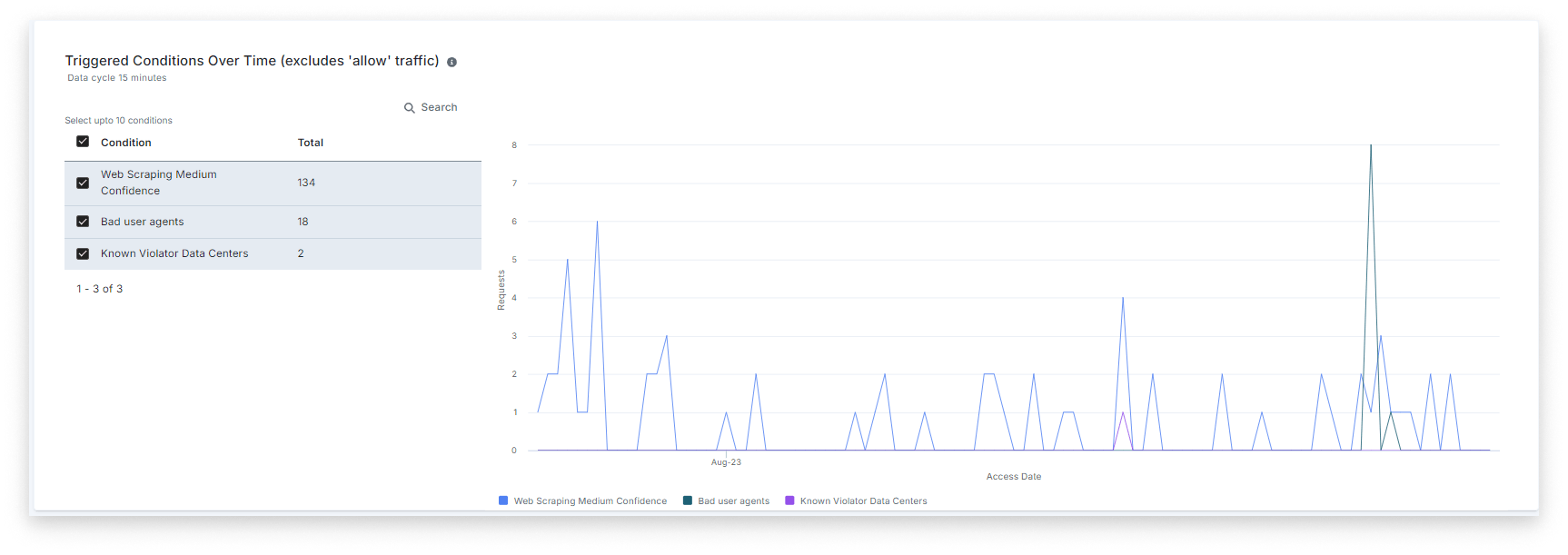
Advanced Bot Protection empowers customers with robust reporting and real-time testing tools. These provide a clear guide for policy creation, false positive analysis, and strategy refinement. Real-world testing in a production environment ensures accurate configurations and effective bot-blocking, giving customers confidence in their bot management strategy.
Organizations can no longer afford to ignore bots. Most are not benign; they are abusing your business. Any functionality on your website is a potential target of malicious bots. Imperva Advanced Bot Protection protects from all OWASP Automated Threats. By blocking bad bots, Imperva helps reduce fraud and business abuse.
Mitigate bot risks effectively by managing bot-accessible content, preventing automated fraud, and eliminating fake interactions.
Defend against layer 7 DDoS attacks, reduce unnecessary infrastructure costs, and simplify compliance efforts.
Lower response efforts, avoid chargebacks, and stay clear of regulatory penalties.
Stop competitors from targeting your applications, scraping your proprietary content and pricing, and damaging your reputation.
It’s great that you’re already using WAF and DDoS protection. But while WAFs and DDoS protection are essential, they often focus on general traffic filtering and volumetric attacks. Advanced bots are more sophisticated and can mimic human behavior, making them difficult to detect with traditional tools.
Advanced Bot Protection is designed to identify and mitigate these advanced bots that slip through other defenses, ensuring comprehensive protection for your online assets.
CAPTCHAs and rate-limiting are basic tools that can stop some bot activity, but they’re often bypassed by sophisticated bots. Plus, they can frustrate legitimate users, leading to a poor user experience.
Advanced Bot Protection goes beyond these methods by using behavioral analysis, device fingerprinting, and other advanced techniques to identify and block bots without disrupting your users.
By accurately identifying bots, our solution can eliminate the need for CAPTCHAs in many cases, leading to a smoother and more user-friendly experience for your customers.
Many businesses don’t realize the extent of bot traffic on their websites until they start monitoring it. Bots can perform a range of malicious activities, from scraping content and pricing data to account takeovers and skewing analytics.
Our latest Bad Bot Report shows that bots account for a majority of web traffic. Even if you haven’t noticed a problem yet, it’s likely that bots are already impacting your site in ways that aren’t immediately visible.
Advanced Bot Protection was designed with customer experience in mind, ensuring your legitimate users aren’t impacted in any way.
Our solution uses advanced machine learning algorithms to accurately distinguish between bots and legitimate users, and stop the most sophisticated automated threats with the fewest false positives.
We also offer customization options that allow you to fine-tune the detection rules based on your specific traffic patterns, further reducing the risk of false positives.
Even if you choose to serve a CAPTCHA as a response option, rather than blocking, legitimate users are not served a CAPTCHA on 99.999% of requests when it is selected by our customers as a response option.
We understand that performance is critical, especially for user experience and SEO.
Advanced Bot Protection is designed to operate with minimal impact on site performance, using real-time analysis that doesn’t slow down your site.
Bot management involves the detection, analysis, and mitigation of automated bots that can threaten your website, APIs, or mobile apps. Effective bot management is crucial to protect your online assets from sophisticated threats like data scraping, fraud, and service disruption.